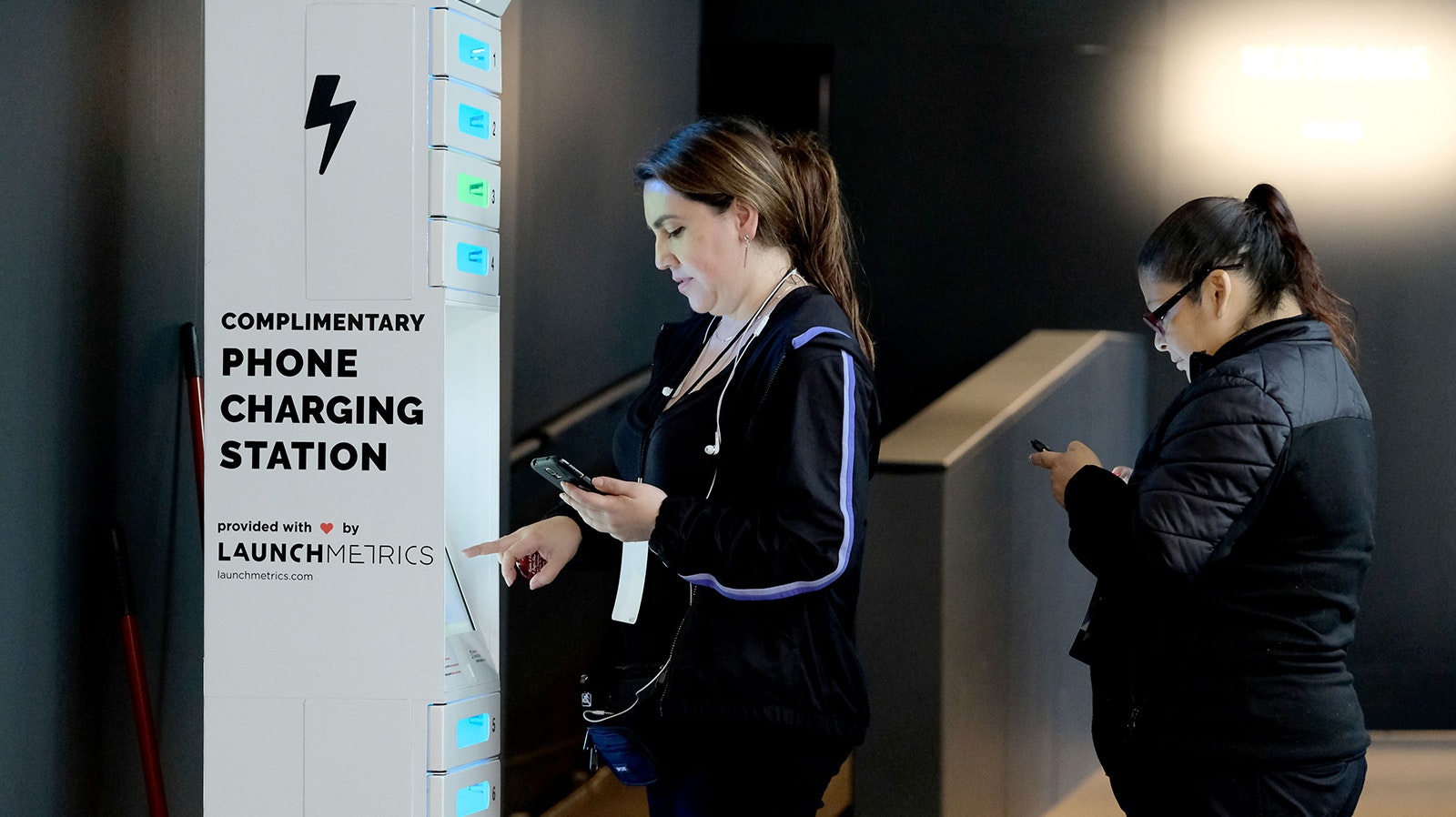
Public charging stations for cellphones and other electronic devices present opportunities for hackers, according to recent warnings from the FBI.
It’s called “juice jacking,” and Wyoming cybersecurity experts say it’s entirely plausible the public charging ports commonly found in airports, libraries, bars and other public places could be used to install malicious software or steal data from phones.
“The charger port on a phone is a data port. So, if you plug your phone into your computer, your computer will detect it as a browsable device,” said Elmer Robinson, owner of Cheyenne-based Rocky Mountain Cyber Security.
Bad Actors
The Federal Communications Commission began warning about juice jacking as far back as 2021.
“In some cases, criminals may have intentionally left cables plugged in at charging stations. There have been reports of cables being given away as promotional gifts,” an FCC statement warns.
The FBI and FCC advise people to avoid using free charging stations in airports, hotels or shopping centers, and that people should use their own chargers and USB cords plugged directly into electrical outlets.
They also warn that if you plug into a USB port and get a prompt asking you to “share data” or “charge only,” definitely don’t select the “share data” option.
“Bad actors have figured out ways to use public USB ports to introduce malware and monitoring software onto devices that access these ports,” the FBI warns in a statement on its website.
While it leaves out details on exactly how these “bad actors” hijack the ports, Dan King, CEO of K2 Technologies, which has offices around Wyoming, told Cowboy State Daily that hackers likely install a fake port inside the public port at a spot that’s not visible or well trafficked.
“It does take a little bit of work to install one, at least from the research I’ve done,” King said. “It’s just an add-on to the little USB port that you’d normally plug your cable into. You think it’s just a charging cable, but it can transfer data.”
Bring Your Own Cable
Dan Catone, CEO of Golden State Wealth Management, moved from California to Powell in 2018 because he liked the friendly atmosphere of the town and business-friendly environment of Wyoming.
He has to travel a lot for his job, which means he spends a lot of time in airports using his cellphone. He said the company’s chief information officer, Clint Nylander, is very security conscious and advises employees not to plug anything into a computer if they don’t know where it came from. The same goes for plugging something into a phone.
“The idea of plugging a USB cable into a phone as I’m traveling, especially for business, I would never do that,” Catone said.
He would, though, plug his own charger into an electrical outlet, which is safe from hackers.
Everything Is Hackable
Rob Miller, Cowboy State Daily columnist, has another way to beat hackers. He still carries an old flip phone, technology too outdated to be vulnerable to juice jacking.
Smartphones, which are almost universally preferred nowadays, are not as secure.
“Everything's mini-USB kind of plugs now. They’re all fairly standard, and they’re all data ports, in addition to being charging ports,” Robinson said.
King said iPhone users shouldn’t assume they’re secure. Apple has a lot more restrictions on what apps can be used on its devices, which makes those devices more secure than Windows and Android devices.
But King said where there’s a will, there’s a way.
“Everything is open to being hacked,” he said. “Let’s just put it that way.”